Unwanted calls can be a real nuisance, which is inconvenient and annoying at the best of times, especially for the elderly or vulnerable it can be quite frightening. It is a “plague” not only for individuals but also for companies. Mobile phone users can install some blocking Apps to filter and block specific numbers easily, however, for companies, how to protect extensions from this nuisance?
With Blocklist/Allowlist feature, Yeastar S-Series VoIP PBX and Yeastar Phone System can easily help you get rid of them once and for all. In this blog posts, we’ll give a comprehensive introduction into this feature, about how it works and how to configure the feature on Yeastar PBX.
#1 Call Blocklist
The blocklist feature of Yeastar phone system functions similarly to call blocker apps on your mobile phone, but there are still some differences.
Call Blocklist is used to block incoming and/or outgoing calls. If you list a phone number of the incoming call in the blocklist, you will not receive the call from this number any longer. And the caller will hear the following prompt: “The number you have dialed is not in service. Please check the number and try again”. The system will then disconnect the call. Likewise, if you list the phone number of the outgoing call in the blocklist, you can not dial that number any longer.
Blocklist groups
Nuisance calls are varied and usually attempt to promote a product, service to you, or even defraud you. Categorizing the blocklist call by name will greatly help companies optimize phone management.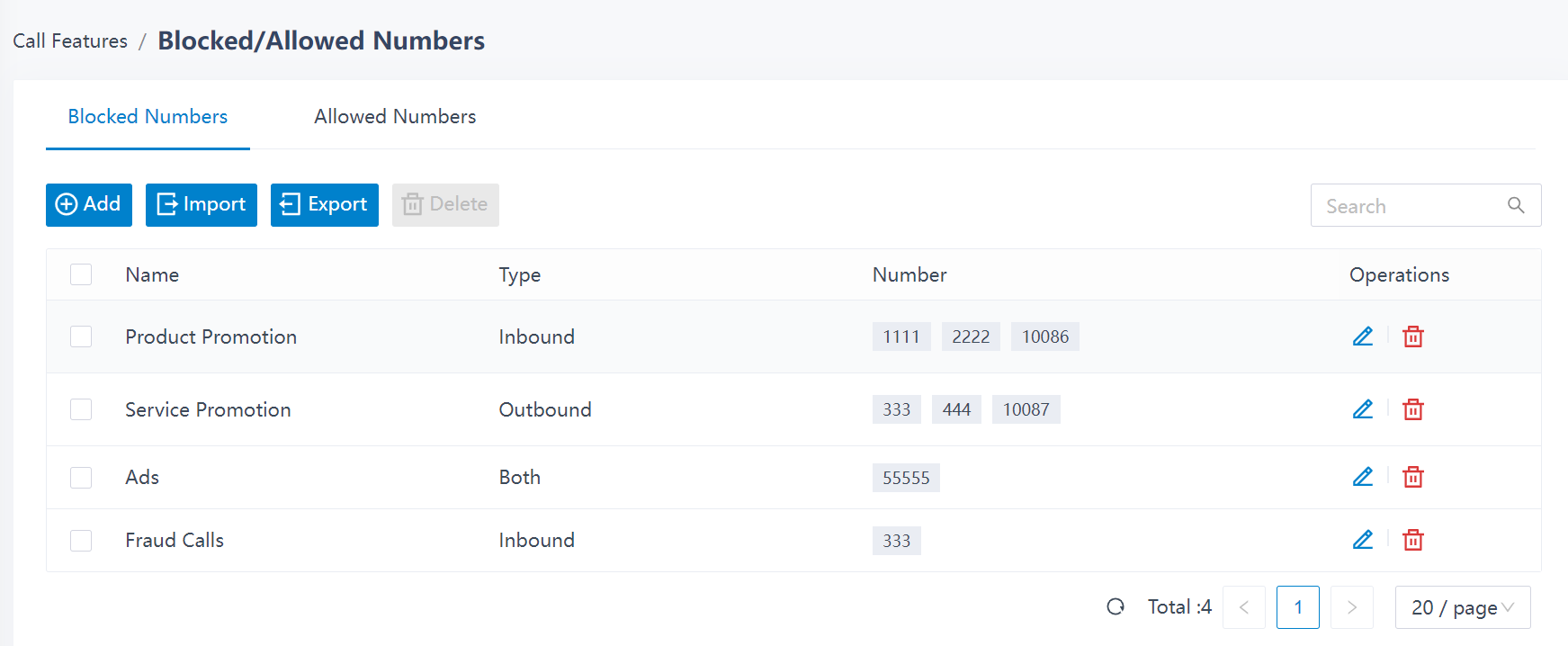
Block Calls Based on Phone Number
Yeastar phone system allows you to route or block incoming calls from internal or external users by phone number. You can customize different call handling rules for each extension/Caller ID. Also, you can set up a blocklist for the phone system, which means all the PBX extensions can NOT reach or be reached by the phone number.
Note: System blocklist has higher priority than individual blocklist.
Block Calls with Number Segment
It can be easily found that lots of nuisance calls are of same number segments. In this case, you can use the wildcard matching to flexibly block the phone number with specific segments by setting call blocklist rules.
For example, if you enter “400.” (where the wildcard “.” matches anything remaining) in the number field as shown below, the system will block all unknown numbers of any length beginning with 400. Similarly, by entering “95XXX!” (where “X” matches any digit from 0-9 and the wildcard “!” causes the matching process to complete), the system will block all five-digit numbers beginning with 95.
Note: the wildcard rules are defined by the phone system by default.
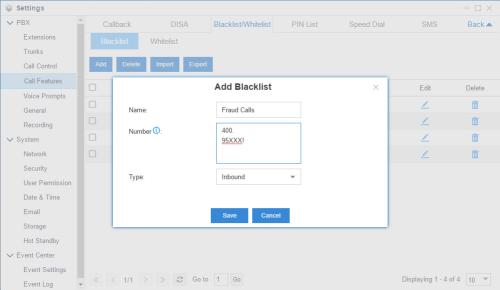
Add Blocklist on Yeastar PBX System
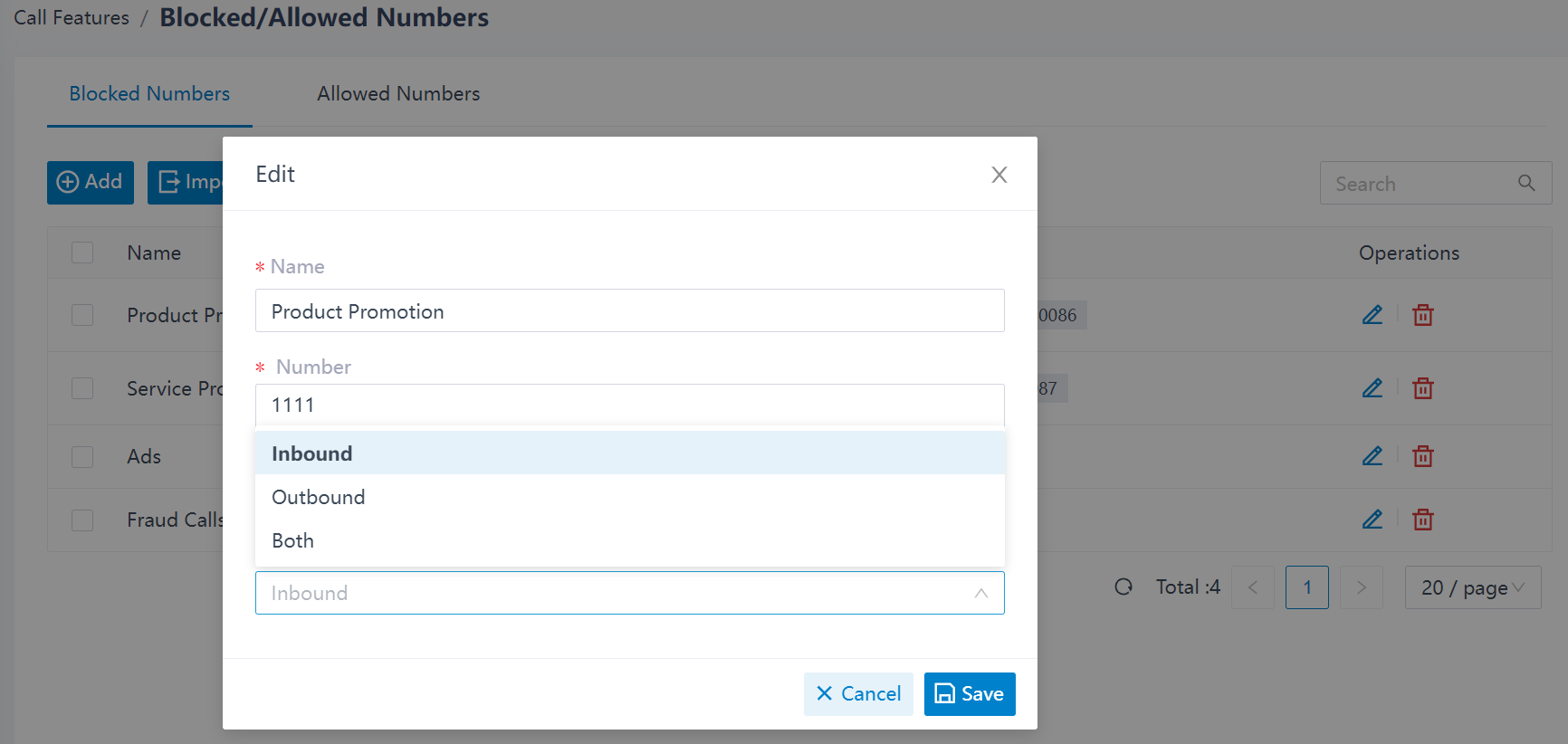
Blocklist Types
In addition to some unwanted calls, you may also encounter “one ring call”. If your phone rings once, then stop, think very carefully before calling that number back because your phone may face high charges. Such “ring-back” or “ one-ring” scams have long plagued the telecom world. With Yeastar, you can also prohibit your extensions to make outgoing calls to these numbers to avoid huge losses.
Yeastar phone systems support to block or allow 3 types of calls/numbers:
- Inbound: Disallow or allow the number to call in the PBX system.
- Outbound: Disallowe or allowe extension users to call the number out.
- Both: Both inbound and outbound calls of the number are disallowed or allowed.
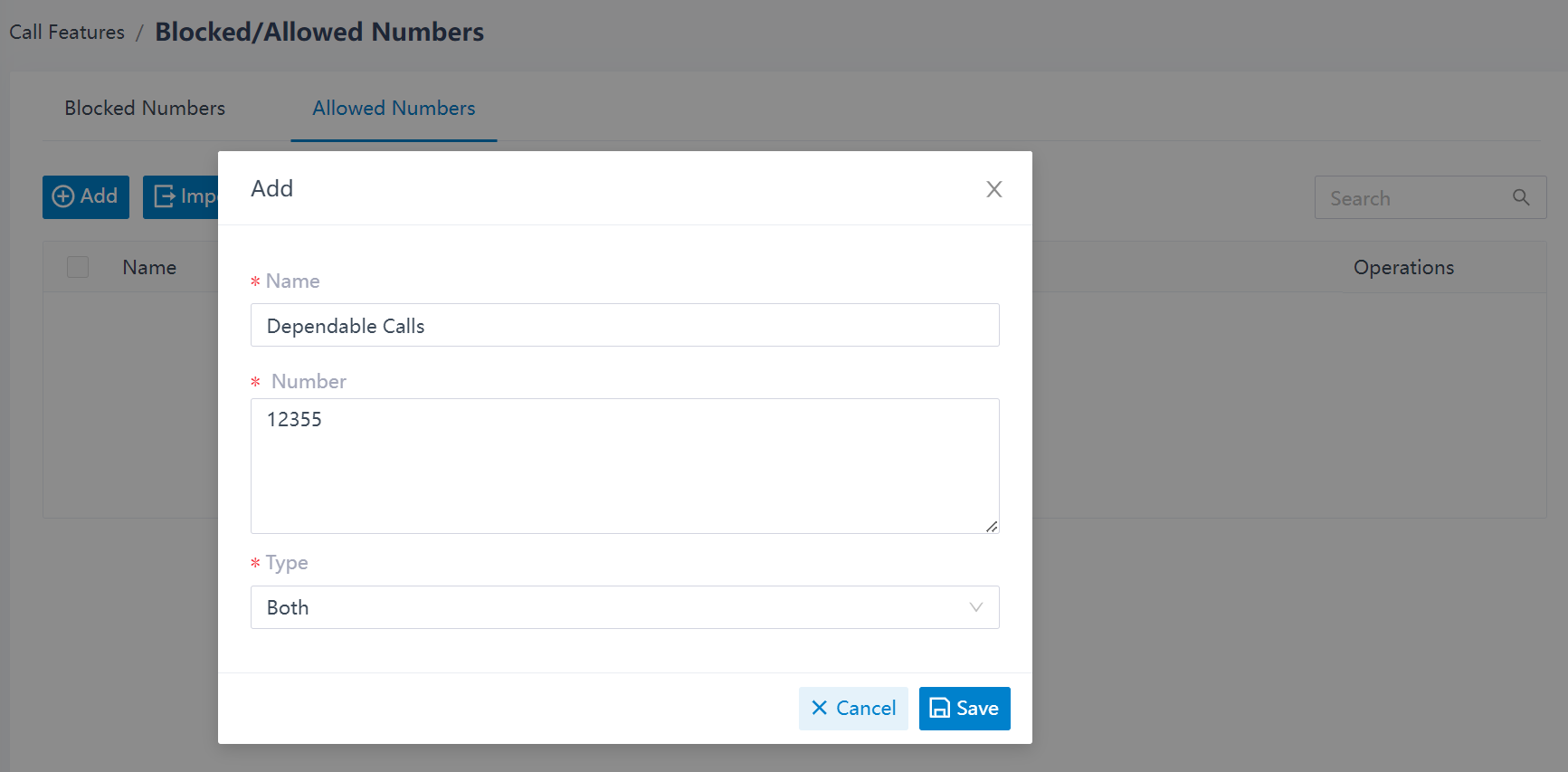
#2 Call Allowlist
If trusted phone numbers happen to be listed in system blocklist, you can add the trusted phone numbers to system allowlist. Numbers in the allowlist are allowed to dial in, dial out, or both. And the feature also support both individual and system levels.
The trusted incoming/outgoing numbers in Yeastar Phone System and S-Series VoIP PBX have higher priority than the blocklist.
For example, we listed all phone numbers beginning with 400 in the blocklist via the “400.” blocklist rule, however, your customers’ phone number happens to be 4005915259. Simply by adding this number in your allowlist, you can make/receive calls from this number while blocking other numbers started with “400”.
#3 Blocked/Allowed Number Management
The blocked/allowed numbers added on Yeastar phone system can be exported and saved as a template. You can fill in desired numbers information in the exported file, and import the file to the phone system quick and easily.
You can also delete the added numbers in bulk if you no more need to block or receive these numbers. Just some simple clicks in the pop-up windows will be ok.
Learn More: Manage Blocked Numbers | Manage Allowed Numbers
You might be also interested in:
In addition to the blocklist/allowlist feature, Yeastar phone system also provides auto call recording feature to automatically save the conversations of the fraud calls. This can provide dependable evidence for tracing the criminals.
You can also gain a comprehensive into Yeastar VoIP PBX features here. We not only list the features but also explain each with uses case, configuration video guides and etc.

how to block call from “Unknown” number ?
Hi Dendi,
Blocking calls from unknown numbers in your phones, you can click here for reference. Blocking calls from unknown numbers in PBX, you can refer to the post.
I think dendi is trying to say, and I also want to know, how can I block an unknown number, when no number appears on the screen? But at the same time, letting in calls from numbers that I don’t have on the list
Hi Fran, to solve the problem, you can edit inbound route, adding “X.” and “+X” into Caller ID pattern therefore the unknown ID will be blocked automatically. For more details, you can send mail to this address helpdesk@yeastar.com. Our support team will help you asap.